With the expansion of the Internet of Things come increased cybersecurity concerns. The technology is finding its way into every industry, elevating connectivity and making our lives easier. However, there are downsides to this, and ever-growing connectivity is becoming more of a problem as cybercriminals seek to exploit it.
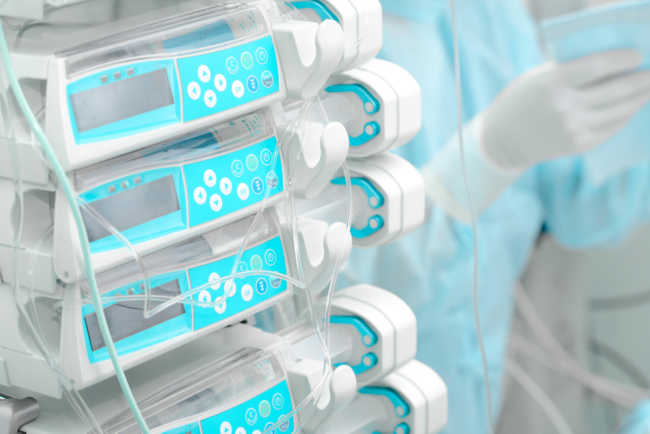
Perhaps this is most visible in the medical industry, where patient data security is of utmost importance. Regardless of it being a top priority for healthcare providers, patient data frequently gets compromised. This is why it’s imperative to secure IoT medical devices by preventing malicious exploits and adopting various security-related procedures. Let’s have a closer look at the requirements for securing IoT medical devices. Find more about IoT: Three Types of Security
What Manufacturers Are Doing to Secure IoT Medical Devices
For manufacturers of medical devices, it’s crucial to stay on top of the latest trends that make it easier to implement higher cybersecurity measures. They devote plenty of attention to integrating multicore system-on-chips or SoCs into their designs because there is an increasing need for systems to process information and tasks quickly. It’s especially important to choose the right silicon for the material of the processor, as well as to include processor security features. Secure boot and boot fuses, device partitioning and crypto engines are used to prevent different kinds of possible cybersecurity problems.
There’s also the implementation of Linux as the operating system that fits with medical devices best. Thanks to its proven toolchains and APIs, Linux is safer than most operating systems, and it’s also feature-rich. Another critical challenge for the medical device manufacturers and developers is making sure that IoT doesn’t make it easier for cybercriminals to invade the system despite increased connectivity. There are different ways in which they are doing that.
Protecting the IoT Medical Devices
Developing security for a medical IoT device is no easy task. Those in charge of it need to assess weaknesses in the system and determine what’s the surface area that’s most vulnerable to cyber attacks. To prevent cybersecurity issues, developers need to take a look at the three stages of data security.
How to Secure IoT Medical devices:
Data at rest
From the moment when a device is being powered to the point when it’s fully operational, data has vulnerabilities. Possible measures to take in this stage are related to the security of storage, the root of trust and chain of trust. The heart of trust and chain of trust need to be established (through software-based solutions if need be) and storage security should be kept on a high level, with anti-tampering methods and proper storage of the bootable image.
Data in use
When the device is operating normally processing and generating data, the data is vulnerable to attacks. Developers can improve cybersecurity in this stage by using hardware-enforced isolation, software-enforced separation, userspace isolation or information and data obfuscation. Physically isolating application by keeping multiple SoCs side by side is an excellent solution for those who can afford it. Alternatively, you can separate applications by using software solutions and add another level of security by obfuscating the data.
Data in transit
When the device is on, and data is leaving or entering it; data might be at its most vulnerable. In this stage, it’s important to make sure that the receiver of information has been adequately identified by using mutual attestation. In case that fails and the device gets hijacked, developers have to ensure that data is still protected by encrypting it. That’s usually accomplished by using SoCs with crypto engines that are quite difficult for hackers to crack.
Conclusions
For any conscientious IoT medical device manufacturer and developer, cybersecurity should be at the top of the list of priorities. A specialized IoT security partner is your best choice to help you reach and maintain your IoT security goals “while minimizing your costs and the security risks.”
More about Top cybersecurity challenges in the healthcare industry
The Importance of Security by Design for IoT Devices
Originally this article was published here.
![]() This article was written by Roland Atoui, Managing Director & Founder of Red Alert Labs, expert in Information Security and Certification with more than 10 years of experience in the industry. From smart cards to smart phones to smart manufacturing, Roland is a new technology enthusiast with a current mission to bring trust to the Internet of Things.
This article was written by Roland Atoui, Managing Director & Founder of Red Alert Labs, expert in Information Security and Certification with more than 10 years of experience in the industry. From smart cards to smart phones to smart manufacturing, Roland is a new technology enthusiast with a current mission to bring trust to the Internet of Things.