Securing Automation: Why the Specification Stage Is the Right Time to Embed OT Cybersecurity
Manufacturers are excited about 2026. The latest Sikich Industry Pulse shows that 65 % of respondents feel pressure from rising demand, 56 % are planning new equipment and automation projects, yet only 19 % intend to invest in cybersecurity. This…

Cybersecurity Upside Down: Why Detection is a Losing Game for ICS in 2026
The industrial sector is at a crossroads. As we navigate 2026, the traditional “detection-first” mindset that has governed OT (Operational Technology) cybersecurity for decades is proving insufficient against the rise of autonomous, AI-driven threats.During an interview at S4x26 in…

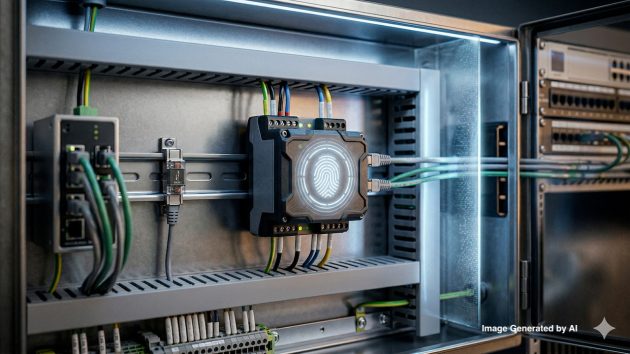
Six ICS/OT Cybersecurity Solutions for 2026: Securing the Air Gap
In 2026, the traditional “air gap” is a logical challenge. The convergence of IT and OT, coupled with AI-driven threats, has rendered “security by obscurity” obsolete. To maintain operational resilience, industrial leaders are shifting their focus…

AI in Manufacturing Introduces a New Risk: Can You Trust What the Model Learned?
Why AI risk in factories is no longer just a cybersecurity issueManufacturers are beginning to use AI in areas that influence real operational decisions: quality analysis, anomaly detection, process optimization, and predictive maintenance. As this accelerates,…

Why Your AI Strategy is Failing the Audit: The Provenance Gap in Manufacturing
In the race to automate, many manufacturers are hitting a wall. It is not a lack of processing power or a shortage of LLMs. It is a trust problem. The “bottleneck” to scaling AI in the…

The Shop Floor Is Still the Weakest Link in Industrial Cybersecurity
Why modern factories remain dangerously exposedManufacturers invest heavily in IT security, cloud controls, and compliance frameworks. Yet once you step onto the shop floor, a different reality often appears. Industrial environments still contain machines that communicate…

January 2026 Industrial IoT & ICS Cybersecurity Events
New year, new budgets, and a fresh slate of industrial priorities—secure connectivity, resilient operations, and scalable modernization. January 2026 offers a compact and high-impact set of gatherings where Industrial IoT (IIoT) and ICS/OT cybersecurity conversations show up in different forms:…

Secure-by-Design Manufacturing: Why Compliance Is the Next Competitive Edge
Digital transformation has turned factories into networks of connected assets, data flows, and intelligent systems. But every new connection expands the attack surface — and with it, the risk. For manufacturers, cybersecurity is no longer just…

Securing the Connected World: IoT Cybersecurity Challenges and Policy Priorities for 2025
The Internet of Things is no longer a fringe technology. Sensors, cameras, medical devices, industrial controllers, smart meters, and connected vehicles are now integral to how we live, work, and defend our nations. IoT promises enormous…

November 2025 Industrial IoT & ICS Cybersecurity Events
As November 2025 unfolds, a dynamic lineup of Industrial IoT, manufacturing, and cybersecurity events is set to inspire innovation and collaboration across the global industrial landscape. From automation and smart manufacturing to AI, GxP compliance, and…