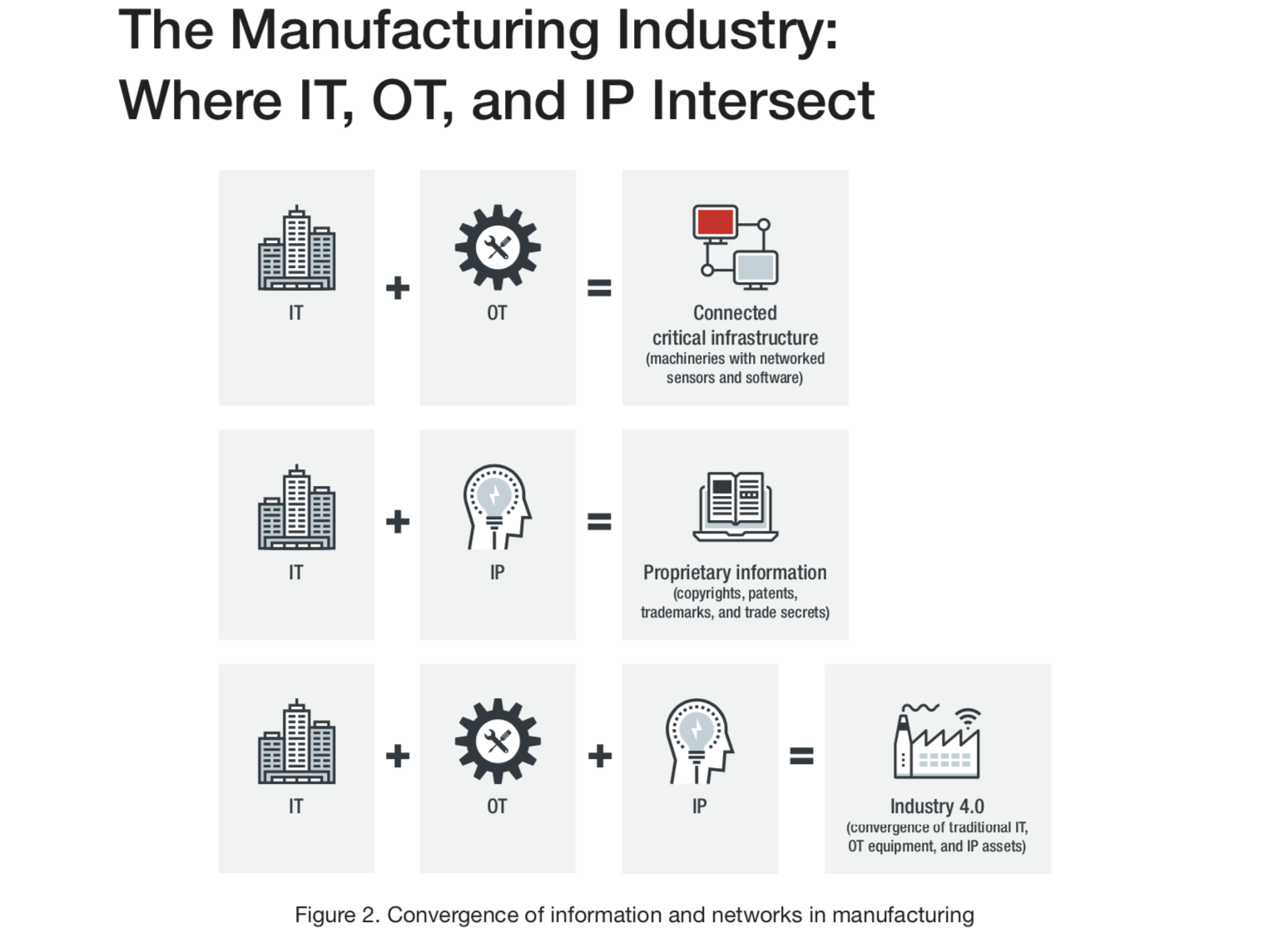
Adopting Industry 4.0 means not only interconnecting IT and OT networks to build smart factories; it also means having shared responsibilities between IT administrators and OT engineers. These include accounting for assets such as equipment, underlying platforms, and protocols or services in use; assessing them for their criticality in the overall operations; and applying the appropriate protection to each asset.
In addition to ensuring that the aforementioned tasks are carried out, manufacturing companies also need to see to it that IP assets, such as technical documents and design files, are being shared, processed, and otherwise handled securely.
Manufacturing companies can avoid common security issues by implementing basic best practices such as the following:
- Individuals who are granted access to files and systems should be identified and given the most restrictive permissions. If they should not be able to modify information, read-only access should be given to them.
- The IT machines and production machines that are allowed to communicate with one another should be identified. There should be restrictions as to which devices in the IT network should be capable of information exchange with which devices in the OT network.
- Unnecessary services in the network should be disabled. Doing so can help prevent exploitation of vulnerable services.
Security is critical to the success of Industry 4.0 adoption. The resilience of production processes strongly depends on the manufacturing companies’ awareness of the current threat landscape and the employed security framework for protecting against attacks. More about: Security Architecture for Smart Factories
Download the “Securing Smart Factories in the Era of Industry 4.0” research paper published by Trend Micro to find out what are the most noteworthy threats to the manufacturing industry. Also, the research identifies the weak points that attackers may take advantage of, and provides relevant security recommendations. Please also check Top 20 Internet of Things Research Frontiers of the Leaders
Here is a short overview of the content you will have access to by downloading the paper:
- IT Network Threats
- OT Network Threats
- IP Threats
- Underground Activities Related to the Industrial and Manufacturing Sectors
- Consequences of Security Breaches
- Security Recommendations
- Conclusion
![[Research] Securing Smart Factories in the Era of Industry 4.0](https://iiot-world.com/wp-content/uploads/2019/06/internet-technology-cyber-security-concept-protect-scan-computer-virus-attack.jpg)


