Fortinet has worked with Forrester Consulting for a third time to check in on security trends affecting those who manage and maintain critical infrastructure—including the industrial control systems (ICS) and supervisory control and data acquisition (SCADA) systems that manage everything from factories to refineries to telecommunications infrastructure. Based on a global survey, the report identifies four trends:
• Organizations are moving more deliberately than expected in the convergence of IT and operational technology (OT) systems. The primary reason for this seems to be to ensure the security of critical infrastructure .
• Critical infrastructure professionals have many security concerns, including emerging risks from Internet-of-Things (IoT) devices and ongoing and growing priorities centered on compliance. More about Managing the Risks of Digital Transformation
• The typical organization has not deployed a strategic, integrated approach to OT security, instead deploying multiple technical point solutions on different timelines, and in some cases, relying on one or more third parties to cover specific aspects of security .
• Organizations tend to find themselves stuck in a reactive stance toward security, and as a result, the vast majority have suffered breaches in their ICS and SCADA systems—many as recently as the past 12 months .
The good news is that respondents seem to recognize the need for a more strategic approach, and a few companies have adopted best practices that have enabled them to avoid OT system breaches over the past two or more years . This provides a glimmer of hope for the future as organizations scramble to address emerging threats .
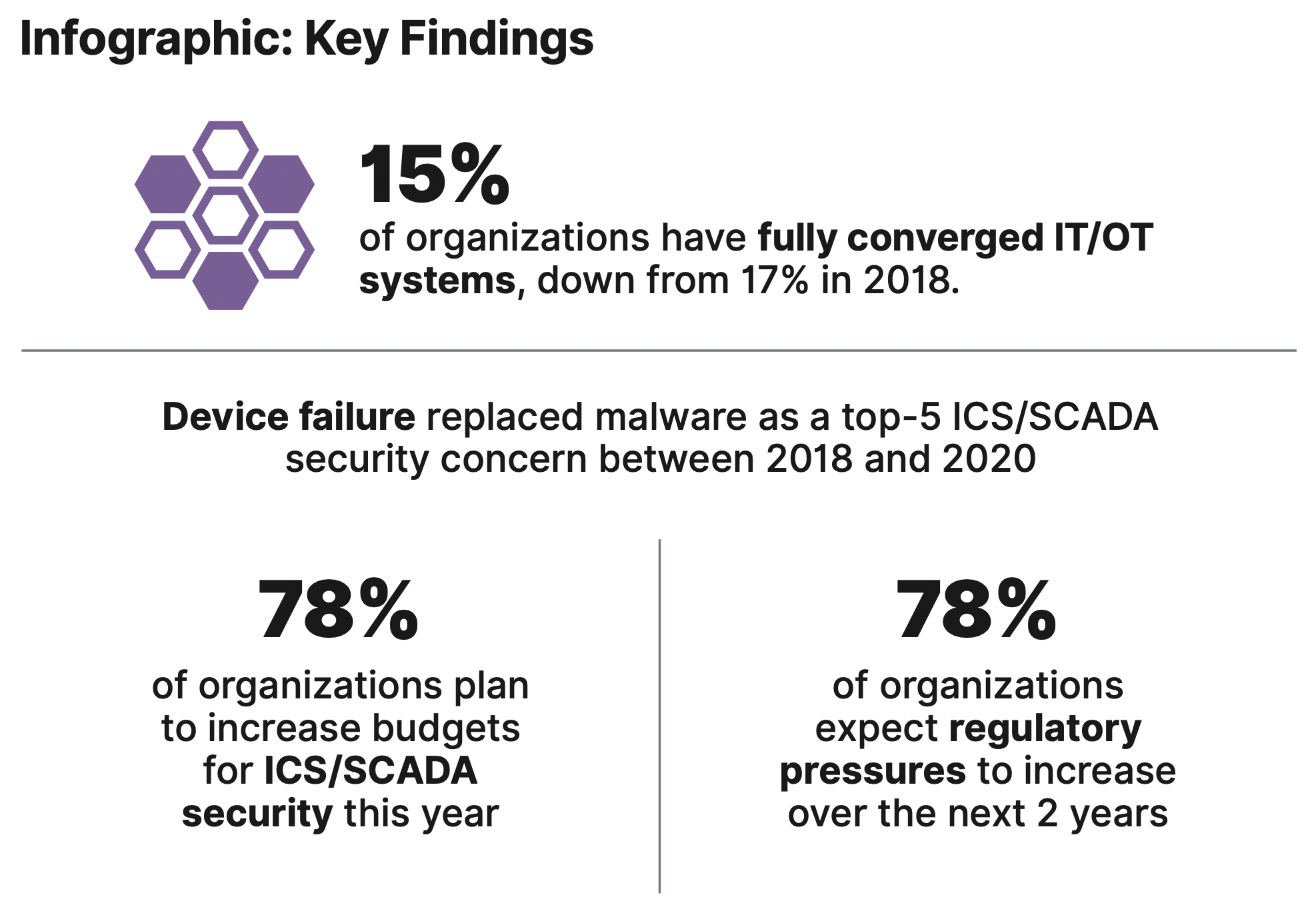
Table of Contents
– Infographic: Key Findings
– Introduction
– Methodology for This Study
– Critical Infrastructure Cybersecurity Trends
– The Convergence of IT and OT Is Complex, and Organizations Are Moving Deliberately
– Those Protecting Critical Infrastructure Have Many Security Concerns
– Securing ICS/SCADA Systems Is Complex and Haphazard Approaches Are Not Uncommon
– OT Security Tends to Be Reactive, and Most OT Systems Have Suffered Breaches
– Best Practices of Top-tier Organizations
– Conclusion
– References
![[Report] Security Risks Are Slowing IT-OT Convergence](https://iiot-world.com/wp-content/uploads/2022/05/Security-Risks.jpg)


