Securing IT and OT in Industrial and Manufacturing Environments
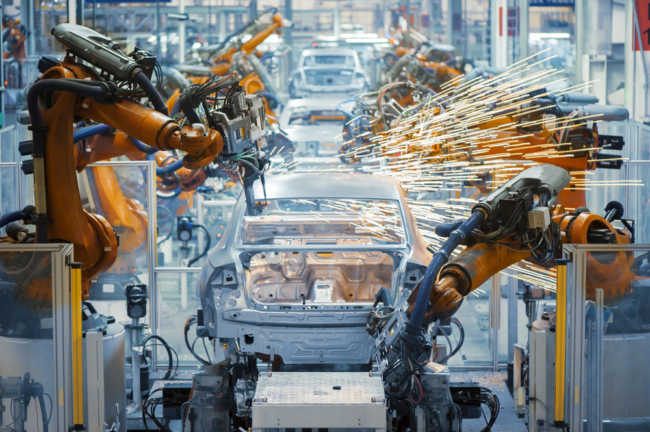
For many years, industrial control systems—often called “Operational Technology” or OT—have been relatively safe from cyber attacks. The control and telemetry systems used in industrial plants and manufacturing environments were typically placed on isolated or “air gapped” communication networks, and the systems themselves were based on highly specialized operating systems which were difficult to attack […]
Read more →