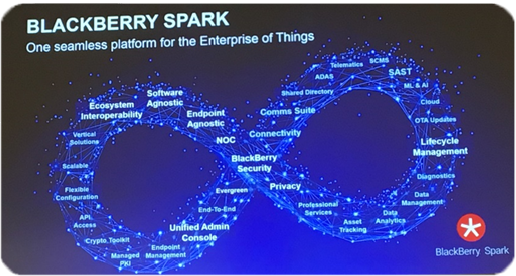
All Endpoints Are Not Created Equal, But They All Need Protection
What you are about to read could be straight out of a horror movie. You would hear the eerie voiceover intoning…”In a world where endpoints are under constant attack, how do you protect yourself? Your critical infrastructure? Your data? Your business?” It’s a weighty question and a huge topic that probably does warrant an entire […]
Read more →