Trustworthiness methods in Industrial System Design
Trustworthiness in the context of an industrial system is a relatively new term intended to provide a better understanding of the meaning of trust in such a system and how…
Released this week: Global ICS & IIoT Risk Report
Industrial and critical infrastructure organizations that rely on industrial control systems (ICS) to run their businesses — such as firms in energy and utilities, oil & gas, pharmaceutical and chemical…
24 interesting Startups focused on Industry 4.0 to watch out at the Web Summit
ALPHA 2018 has sold out. ALPHA is a program run by Web Summit organizers and aims to spotlight the early stage startups engineering the future, connecting them to the world’s…
[Report] Exposed and Vulnerable Critical Infrastructure: Water and Energy Industries
TrendMicro published research at the end of October revealing how exposed human-machine interface (HMI) systems in thousands of critical water and energy organizations around the world could be exploited, causing…
Critical Infrastructure and ICS Security Remain a Network Segmentation Problem
Companies in every industry are developing and implementing connected industrial control applications as strategic digital business initiatives. However, the risks of security breaches and the subsequent impacts to consumer privacy…
Marin Ivezic, Partner PwC
Marin Ivezic is a Partner at PwC. From his start in law enforcement more than 25 years ago, Marin came to focus on emerging threats of cyber-kinetic attacks – cyberattacks…
Combine Crosser Edge Streaming Analytics and Azure IoT Edge
Based on customer requests we have implemented support for running Crosser Edge Streaming Analytics on Azure IoT Edge. Now you can innovate much faster and without the cost, risk and…
What makes a smart city smart?
Half the world lives in cities. By 2050 that figure will rise to 70 percent, boosted by the 2.2 billion more people who will live on the planet at mid-century.…
The CANOPY WING Vulnerability: Weaponizing the Weakness
Finding a vulnerability, developing an exploit, and then launching (or not launching) this exploit – is repeated many times every day. Now more than ever companies must be aware of…
Navigating the big pivot from IoT to AI-driven analytics
If you’ve worked in industry for any length of time, you’ve experienced wave after wave of digital technologies washing over the plant floor, from robots to tablets. The next decade…
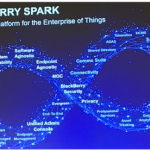
The Transformation of the Tech Sector’s Second Most Famous Fruit Will Spark your Interest
I remember vividly the feel of that little side-wheel spinning rapidly in response to my overly exercised thumb’s pressure. Scrolling frantically through the myriad of emails and messages on my…
Staying secure in the smart era: Three rules for cybersecurity
Almost half of the manufacturers have fallen victim to cybercrime, according to the Cyber Security Manufacturing Report 2018, published by EEF. One of the biggest challenges for manufacturers is choosing…