How to Protect Deployed Assets from Log4j
What Is the Log4j ExploitNearly every week the cybersecurity community buzzes around a newly discovered vulnerability or a breach. December’s alert for the CVE-2021-4428 vulnerability in Apache Foundation’s Log4j software is no different. Also known as…

Cybersecurity Trends to Prepare for in 2022
Recap of Cybersecurity and Cyber Attacks in 2021 Dare I say that the past year has been…drumroll…unprecedented…in the realm of cybersecurity and cyber attacks? Here are some statistics to showcase what the industry has endured over…

Top January 2022 Industrial IoT & ICS Cybersecurity Events
New year, new beginning, new events! There is nothing more exciting than learning something new. And as we start the new chapter of the year, we welcome you with Top January 2022 Industrial IoT & ICS…
Addressing cybersecurity vulnerabilities in the changing LINUX landscape
Linux is a prevalent component of nearly every workload: more than 90% of cloud workloads and 70% of web servers run on it. Like all technology solutions, Linux has continued to evolve over time, potentially opening you up…

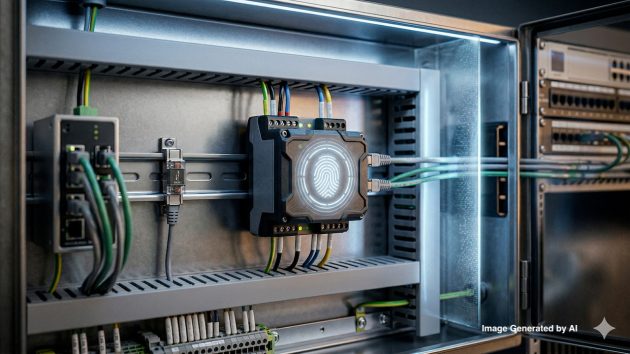
When Industrial Protocol Translation Goes Wrong
A recent research paper delves into the vital role of protocol translation in industrial facilities by looking at the protocol gateway. It is a small device that translates the different protocols used by machinery, sensors, actuators,…

Three main risks that prevent companies from adopting IIoT solutions
The Industrial Internet of Things (IIoT) has brought a lot of benefits and disruptive innovations. Despite this, there are 3 main IIoT project risks that prevent companies from adopting IIoT solutions: IIoT security; lack of open…

Top December 2021 Industrial IoT & ICS Cybersecurity Events
‘Tis the holiday season! ‘Tis the events season! December may be the last month of the year, but it’s definitely not the last when it comes to not-to-miss world-shifting events. Below is the list – and…

Protect Your Organization Against Ransomware Attacks
The following best practices can help focus strategies to protect against this growing threat: Know Your Risks and Plan Accordingly: There are several ransomware attack strategies that organizations need to prepare. Web-based attacks that target and compromise…

Top November 2021 Industrial IoT & ICS Cybersecurity Events
From a deadly pandemic to the face-to-face Web Summit, November is expected to have its fair share of world-shifting events. Here is a list — and timeline — of the major events that happen in November…

5 steps for successful OT endpoint cybersecurity risk management
Operational Technology (OT) has become a heightened target for cybersecurity attacks. The need to address OT (operational technology) cyber risks has never been greater. New threats are emerging every day – both targeted as well as…